Accurate VPN, Relay and Tor Detection
Turn anonymous IP addresses into actionable signals: from a simple boolean flag to full service identification with confidence scoring.
Looking for residential proxy detection? That's a separate dataset with its own methodology.
Accurate Anonymity Detection
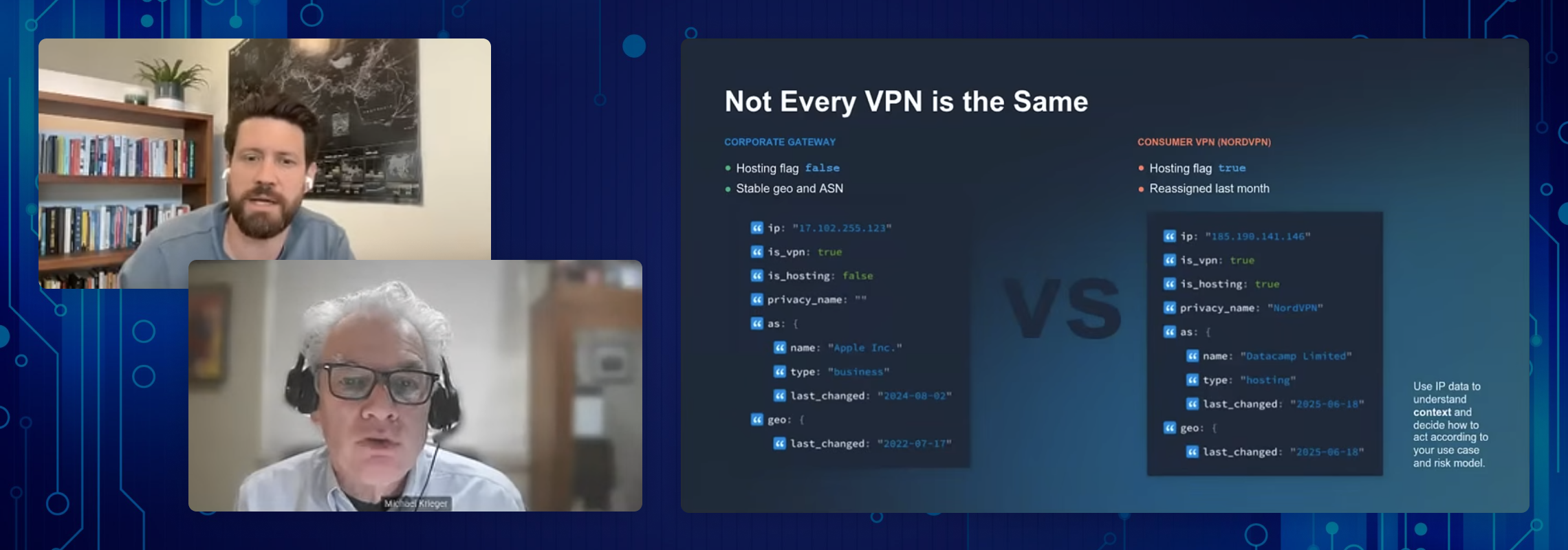
Get actionable privacy context for every IP address. Our proprietary evidence-based methodology flags known anonymizers and hosting infrastructure through active measurement, including VPN and proxy exit node behavior, revealing when traffic may be cloaked or untrustworthy.
With fields like anonymizer type, service name, hosting indicators, and last-seen timestamps, you can quickly determine whether to trust an IP or trigger additional controls. These signals drive better decisions in fraud prevention, security triage, and compliance enforcement.
Unparalleled Accuracy
Our continuously updated database ensures the highest level of precision in identifying privacy-enhancing technologies.
Comprehensive Coverage
Covers VPNs, proxies, Tor exit nodes, relays, and hosting providers. Need to detect residential proxies? That requires a separate dataset .
Easy Integration
Simple REST API with clear documentation and support for multiple programming languages.
Built for rapid, accurate development
Sample Response
Dev Notes
Going to be developing with our data? Here's the main things you may want to know:
One-line setup via curl, fetch, or SDK
Multi-language SDKs (Node.js, Python, Go, PHP, Java...)
Real-time JSON, ~100ms average latency
Optional integrations (API, DBs, Snowflake, GCP, Splunk)
Trusted by Microsoft, WordPress, and 1000s of dev team
Fresh, reliable data with 99.99% uptime, updated daily
Fast and Easy API Access
Gain access to our best-in-class data. Setup takes just a few minutes.
- 50-200 ms response time on average
- 99.999% uptime
- Data updates every 24 hours
- Bank grade security
Custom database download
Leverage raw IP datasets, customize your data feeds, and choose your ideal format.
- Customizable fields
- Data updates every 24 hours
- Bank grade security
Need deeper VPN and proxy insights?
Our Privacy Extended dataset offers over 20 additional attributes designed to reduce false positives and give you more granular detection. View the documentation or contact our sales team to learn more.
What sets us apart from other industry leaders?
We connect to services directly, analyze handshakes, scan protocols, and verify exit node behavior. Every signal is based on direct observation, which means fewer false positives and higher confidence. For residential proxy, which bypass standard privacy detection entirely, we offer a purpose-built dataset built on a separate methodology.
Why Accurate Privacy Data Matters
Effective privacy detection protects more than just infrastructure. It safeguards revenue, ensures compliance, and builds trust. With high-confidence data and broad network coverage, businesses can reliably identify cloaked traffic like VPNs, proxies, and Tor nodes, stop abuse, and tailor user access or content delivery accordingly. For residential proxies, which evades standard privacy detection, IPinfo offers a dedicated detection dataset.
How Customers Use Our Privacy Data
Privacy detection data powers everything from fraud prevention to compliance enforcement. With clear signals for VPNs, proxies, Tor, and hosting providers, teams can make faster, smarter decisions about user trust, risk, and access controls. Here’s how top companies put IPinfo’s privacy detection data to work:
In the realm of fraud prevention, IPinfo's VPN detection API serves as a crucial first line of defense. By identifying connections coming from VPNs or proxies, businesses can flag potentially suspicious activities for further investigation. This is particularly valuable in industries such as finance, e-commerce, and online services where fraudsters often use privacy tools to mask their true location and identity.
In the world of digital advertising, accurate user location and authenticity are crucial for effective targeting and fraud prevention. The privacy detection API enables ad tech companies to refine their targeting strategies and protect their clients from click fraud and invalid traffic. By detecting VPNs and proxies, ad platforms can more accurately geo-target their ads, ensuring that ad content is relevant to the user's actual location rather than the apparent location of a VPN server.
Content delivery networks (CDNs) and websites can leverage the privacy detection API to ensure they're serving the most relevant and optimized content to users. By understanding a user's true location and connection type, even when they're using a VPN or proxy, content providers can make more accurate decisions about content localization, language preferences, and technical delivery optimizations.
The VPN & proxy detection tool is valuable for enhancing threat intelligence. By identifying IP addresses associated with VPNs, proxies, or hosting providers, security teams can better assess the risk level of incoming connections and potential threats. For example, a company's security operations center (SOC) could integrate the API into their SIEM (Security Information and Event Management) system. This integration would allow them to automatically flag and prioritize alerts from connections originating from privacy services or hosting providers, which are often used by attackers to mask their activities.
E-commerce platforms face constant threats from fraudsters attempting to take over user accounts and make unauthorized purchases. The privacy detection API provides an additional layer of security to combat these threats. When a user logs in, the e-commerce platform can use the API to check if the connection is coming from a VPN, proxy, or unusual location. If detected, the platform can trigger additional authentication steps, such as two-factor authentication or email verification.
Obfuscating VPN technologies can provide unfair advantages, such as accessing region-locked content, manipulating server selection for better ping, or bypassing IP-based bans. The privacy detection API also ensures enforcement of anti-harassment and other online safety measures to maintain a fair and enjoyable environment for all players.
Streaming services often have complex licensing agreements that restrict content availability based on geographic regions. Users frequently attempt to bypass these restrictions using VPNs or proxies to access content not available in their region. The privacy detection API provides a robust solution for enforcing these licensing agreements and maintaining compliance.
Made for Developers, Trusted by Enterprises
Our expert in-house team diligently maintains and supports our Privacy Detection, ensuring you always have accurate, up-to-date IP data at your fingertips. With libraries for more than a dozen popular programming languages—from Ruby to Rust and PHP to Perl—integrating our API is quick and seamless. Explore our developer docs to see just how easy it is to get started.
















IPinfo is my silent watchdog as it helps me in pinpointing risk, location & users in real-time
IPinfo was surprisingly valuable and outperformed all the other IP intelligence tools I've tried.
IPinfo is both quick and adaptable and helps us improve our security
IPinfo.io delivers accurate, reliable IP data that strengthens my threat analysis.
Automated IP intelligence by IPinfo helped us streamline our fraud detection.
Why Choose Us?
While many tools rely on outdated data, we utilize our proprietary ProbeNet technology for precise and reliable detection. This powerful methodology gives us the confidence to flag the hardest-to-detect traffic with an accuracy that others simply can't match. Choosing this level of precision safeguards your revenue, ensures compliance, and protects user trust. In today's threat landscape, knowing what's real and what's masked is the ultimate defense.
Further Reading
View allFrequently Asked Questions
Our API detects various privacy-enhancing technologies, including VPNs, proxies (public, residential, and datacenter), Tor nodes, and other anonymizing services. It also provides information about hosting providers.
We pride ourselves on maintaining high accuracy rates, typically above 99% for VPN and proxy detection. Our database is continuously updated, and results are manually verified by our team of experts to ensure the highest level of accuracy.
Our data is updated daily via continuous scans of connections around the world.
Our API is designed for speed, with average response times under 10ms. This allows for real-time integration into your applications without causing noticeable delays. We serve over 4 billion API requests per day!
We offer various pricing tiers to accommodate different usage levels. Our plans range from 150,000 requests per month to unlimited enterprise solutions. We can scale to handle millions of requests per day if needed. Or, if a locally-available database would better serve your needs, we offer our privacy detection data in many popular formats, also updated daily.
Integration is straightforward. We provide clear documentation, libraries for popular programming languages, and RESTful endpoints. Most developers can integrate our API and begin retrieving accurate IP data within minutes.
Yes, our service is designed with privacy in mind. We don't collect or store personal data, and our API usage complies with major data protection regulations, including GDPR. However, it's important to ensure that your use of our API aligns with your own privacy policies and applicable regulations.
Absolutely! We offer a free trial that allows access to a fully-accurate subset of our data. This lets you test the accuracy and integration of our API before committing to a paid plan. You can sign up for a free API key on our website to get started.