Using IP Intelligence to Decode VPNs, Proxies, and Anonymized Traffic: Watch the Webinar
Get Unlimited Access to IPinfo Lite
Start using accurate IP data for cybersecurity, compliance, and personalization—no limits, no cost.
Sign up for freeIn our recent webinar with Dark Reading, I explored how teams are using IP data to understand traffic coming from VPNs, proxies, and other anonymization layers, as well as what that data actually reveals about how traffic behaves in practice.
In the session, I walk through how IP-level signals behave across different types of infrastructure, what can be observed directly from the network, and how those signals are applied in real workflows.
Across the teams we work with, they often progress from basic location checks, then adding privacy detection, and eventually accounting for residential proxies.
If you’re evaluating traffic, investigating activity, or building controls around access and transactions, this context can really shape how those decisions get made.
Watch the full webinar below:
https://www.youtube.com/watch?v=qHcyIQkWu68
Key Takeaways
Geolocation alone doesn’t tell the full story
An IP address might resolve to a specific city, but that doesn’t mean the user is actually there. Anonymized IPs and shared infrastructure break the link between location and user identity.
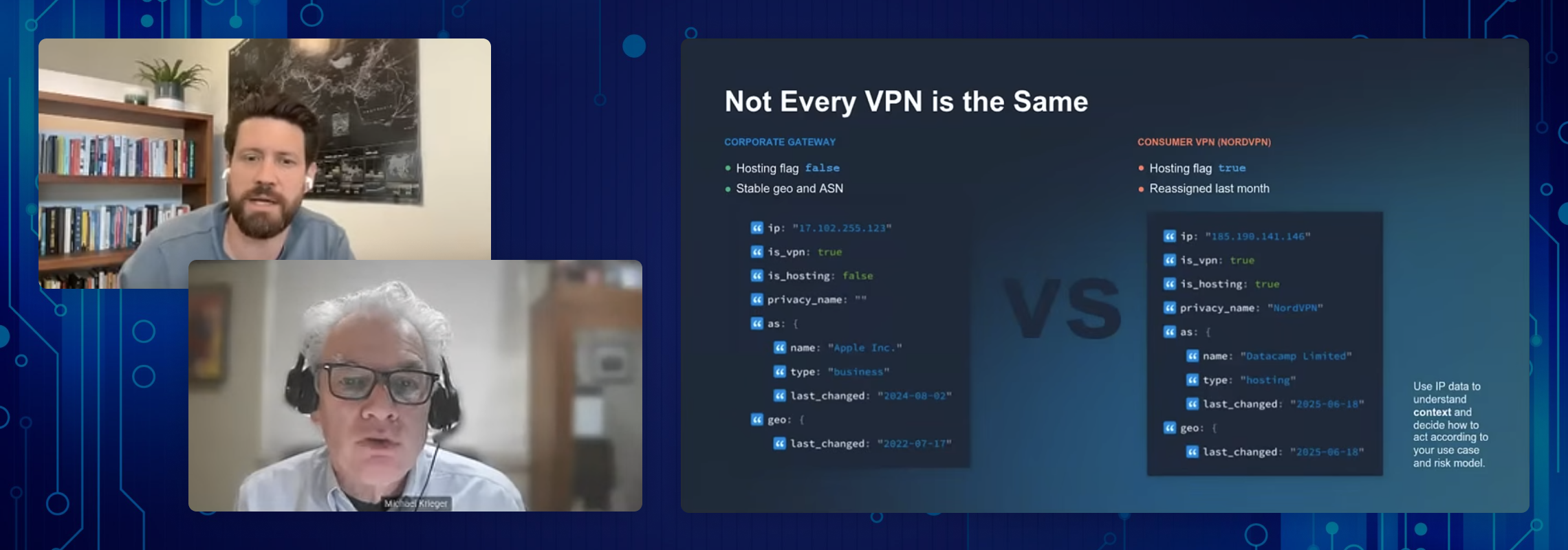
Not all anonymization is the same
A corporate VPN, a consumer VPN, and a residential proxy behave very differently. Treating them as a single category leads to poor decisions and unnecessary friction.
Binary decisions create blind spots
Blocking or allowing traffic based on a single signal (like country or VPN usage) is too blunt. It either lets sophisticated fraud through or blocks legitimate users. IP data can show how traffic behaves, but not the user’s intent, so decisions need to account for that broader context.
Context is what makes IP data useful
Combining signals like geolocation, infrastructure type, usage patterns, and detection flags to build a more complete understanding of each request provides substantial value.
Other tidbits you'll hear:
Why your smart fridge might be a residential proxy. Compromised routers, hacked IoT devices, and even apps that pay users to share bandwidth are how 80M+ real home IPs end up routing fraud traffic.
Why blanket-blocking residential proxies hurts real users. A blocked VPN user just turns it off and retries. A blocked residential proxy user has to leave their house and find a coffee shop to make the payment.
The three-stages of fraud detection: geofence → VPN block → residential proxy detect (and what defenders actually need at each layer)
The IPIDEA takedown wasn't what it looked like. Storefronts went dark, but the network didn't.
Want the full picture? Our white paper, Inside the Residential Proxy Underground, tracks 44.7M IPs across IPIDEA's network: 92.7% also appear in other "competing" providers, and 12 brands share a single Tencent backend. Read the paper
How IPinfo Approaches Anonymized Traffic
At IPinfo, we approach IP intelligence through active measurement.
Instead of relying solely on registry data, we use our proprietary ProbeNet, IPinfo’s internet measurement platform, to actively observe how the internet behaves. That means:
- Verifying where IP addresses actually are located using observed network behavior
- Identifying VPNs, residential proxies, and relays through direct signals rather than inference
- Continuously updating data to reflect how quickly the internet changes
The result is evidence-based context, grounded in measurement, so teams can make more informed decisions about the traffic they see.
About the author

Ben founded IPinfo in 2013 with the goal of providing reliable, easily accessible IP address data. As IPinfo co-CEO, he is committed to constantly improving that data and how customers can use it.